* Disclaimer: This project is a generalized concept based on real-world scenarios. All proprietary data and branding have been removed or adapted.
This project proves the effectiveness of gamification in teaching cybersecurity strategy, visualizing the complex, layered nature of security for a foundational understanding.
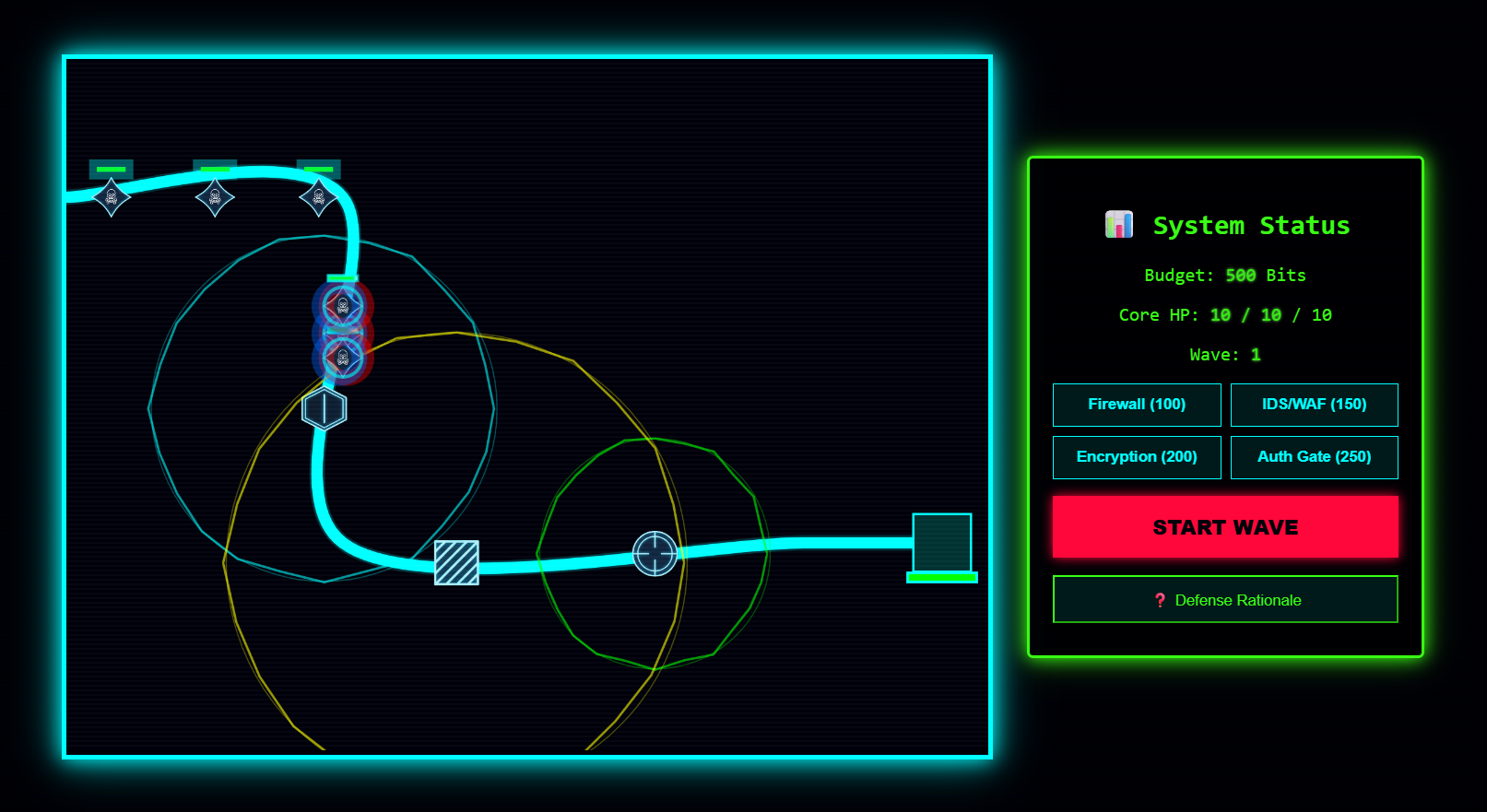
The solution moves beyond passive learning by forcing the user to implement a Defense-in-Depth Layering Model in real-time. Success requires strategic alignment of security controls against specific threat vectors, demonstrating that failure is a direct, measurable consequence of poor strategic planning.
Architecturally, the reliance on p5.js and modular JavaScript ensures high-performance geometric rendering without latency. The project showcases an ability to convert abstract security concepts (like policy and threat mapping) into engaging, measurable behavioral practice that drives superior strategic decision-making.
01. ANALYSIS (THE WHY)
Traditional cybersecurity training often relies on passive multiple-choice tests that fail to build strategic decision-making or demonstrate the functional concept of security layers.
02. DESIGN (THE BLUEPRINT)
I designed a Cyberpunk Data Stream concept to teach DiD principles through visual strategic mapping over a data path.
03. DEVELOPMENT (THE BUILD)
Prototype built using modular JavaScript classes to manage complex game logic and showcase mastery of modern coding practices.
04. IMPLEMENTATION (DELIVERY)
Features accessible instruction via in-game Instructional Pause System and is built for seamless LMS integration.
05. EVALUATION (METRICS)
Success metrics validate the learner’s ability to apply DiD principles strategically, translating directly to educational effectiveness.